
Strava scored B+ (89%) with 148 issues across 7 tested pages, ranking #2 of 8 Testlio portfolio apps. That's 51 fewer than the 199.2 category average (50th percentile).
Top issues to fix immediately: "Header login CTA too subtle on white header" — Increase visual prominence of the login CTA: use a darker background color or outline with a stronger hover/focus state; "DNS resolution failures prevent loading of critical resources (ERR_NAM" — Audit all external resource URLs for correctness and availability; "FedCM get() TypeError: provided value 'widget' is not a valid Identity" — Update the credential request to use a valid IdentityCredentialRequestOptionsMode value or omit mode if optional.
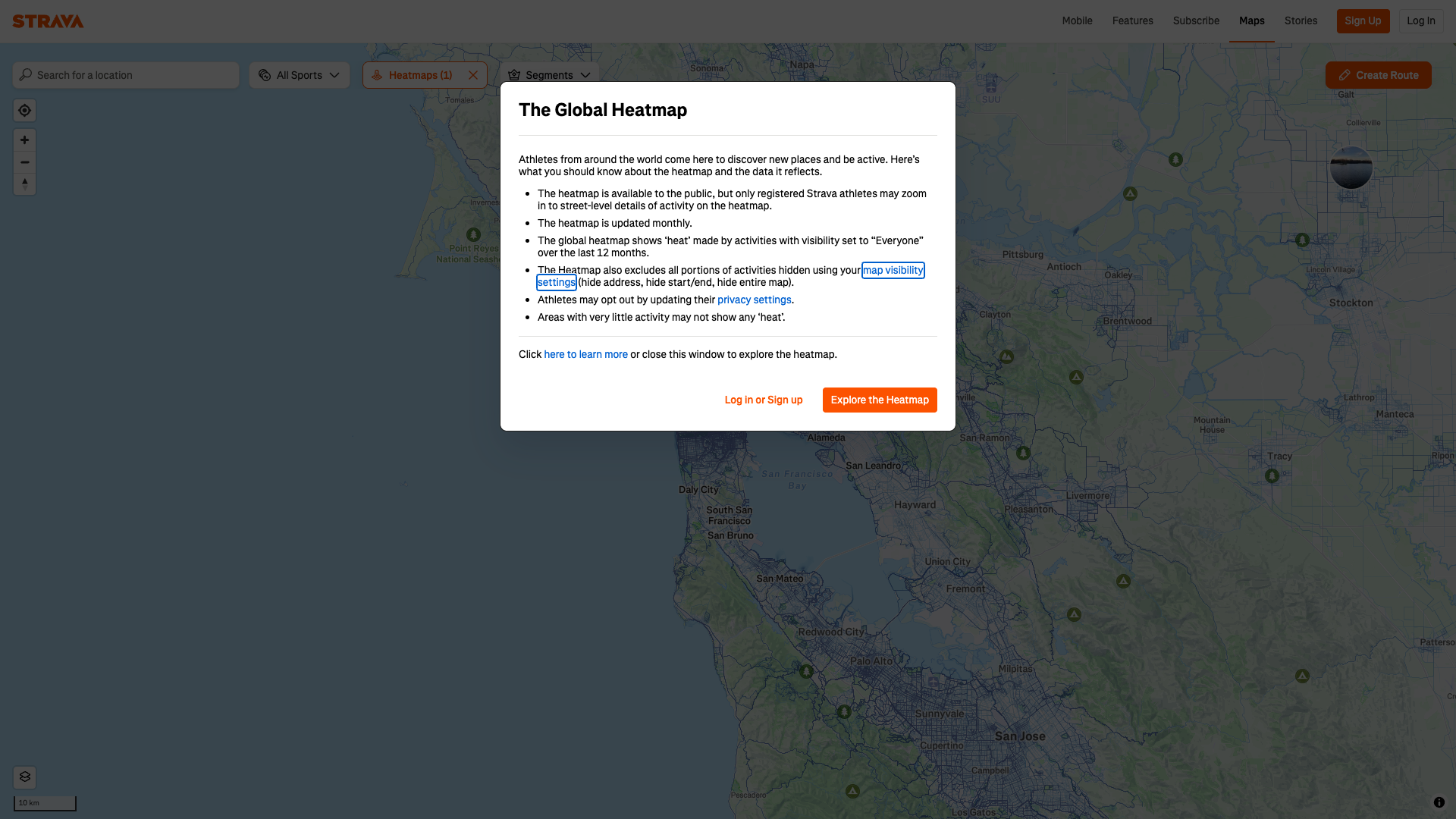
Weakest area — accessibility (6/10): Potential gaps in keyboard navigation and color-contrast considerations; alt text for imagery not visible in this view; needs m...
Quick wins: Improve keyboard accessibility and ensure all images have descriptive alt text; verify color contrast ratios for text.... Add language/localization options and region-specific content to broaden appeal and clarity of benefits.

 Pete · Privacy Networking Analyzer
Pete · Privacy Networking Analyzer⚠️ POTENTIAL ISSUE: Tracking request detectedhttps://connect.facebook.net/en_US/fbevents.js; https://www.redditstatic.com/ads/pixel.js; https://www.googletagmanager.com/gtm.js?id=GTM-TP845S&l=googleTagManagerDataLayer; https://www.googletagmanager.com/gtag/js?id=G-12345&l=googleTagManagerDataLayer; POST https://c.strava.com/com.snowplowanalytics.snowplow/tp2 Sharon · Security Console Log Analyzer
Sharon · Security Console Log AnalyzerAccess to font at 'https://d3nn82uaxijpm6.cloudfront.net/assets/boathouse/Boathouse-Light-ea6efd49dcf4fbc9c0517e6977c97d49ecd6b1ee37d834548ca03d44a3bda882.woff2' from origin 'https://www.strava.com' has been blocked by CORS policy: No 'Access-Control-Allow-Origin' header is present on the requested resource.https://d3nn82uaxijpm6.cloudfront.net/assets/boathouse/Boathouse-Light-ea6efd49dcf4fbc9c0517e6977c97d49ecd6b1ee37d834548ca03d44a3bda882.woff2 Sharon · Security Console Log Analyzer
Sharon · Security Console Log AnalyzerAccess to fetch at 'https://gtm-strava-c81694537.appspot.com/g/collect?v=2&tid=G-12345>m=45je63g1z871715255za20gzb71715255zd71715255&_p=1773789565776&gcs=G111&gcd=13r3r3r3r5l1&npa=0&dma=0&gdid=dMWZhNz&cid=751821140.1773789525&ecid=1625339401&ul=en-us&sr=800x600&_fplc=0&ur=US-WA&uaa=&uab=&uafvl=&uamb=0&uam=&uap=&uapv=&uaw=0&are=1&frm=0&pscdl=noapi&_eu=AAAAAAQ&sst.rnd=1788710205.1773789566&sst.us_privacy=1---&sst.tft=1773789565776&sst.lpc=53990762&sst.navt=n&sst.ude=0&sst.sw_exp=1&_s=1&tag_exp=103116026~103200004~115616985~115938466~115938468~116024733~117484252&sid=1773789527&sct=1&seg=1&dl=https%3A%2F%2Fwww.strava.com%2Ffeatures&dt=Strava%20Subscription&_tu=DA&en=page_view&ep.event_id=17737895661010.2072066568333304&tfd=918&richsstsse' from origin 'https://www.strava.com' has been blocked by CORS policy: No 'Access-Control-Allow-Origin' header is present on the requested resource.https://gtm-strava-c81694537.appspot.com/g/collect?v=2&tid=G-12345>m=45je63g1z871715255za20gzb71715255zd71715255&_p=1773789565776&gcs=G111&gcd=13r3r3r3r5l1&npa=0&dma=0&gdid=dMWZhNz&cid=751821140.1773789525&ecid=1625339401&ul=en-us&sr=800x600&_fplc=0&ur=US-WA&uaa=&uab=&uafvl=&uamb=0&uam=&uap=&uapv=&uaw=0&are=1&frm=0&pscdl=noapi&_eu=AAAAAAQ&sst.rnd=1788710205.1773789566&sst.us_privacy=1---&sst.tft=1773789565776&sst.lpc=53990762&sst.navt=n&sst.ude=0&sst.sw_exp=1&_s=1&tag_exp=103116026~103200004~115616985~115938466~115938468~116024733~117484252&sid=1773789527&sct=1&seg=1&dl=https%3A%2F%2Fwww.strava.com%2Ffeatures&dt=Strava%20Subscription&_tu=DA&en=page_view&ep.event_id=17737895661010.2072066568333304&tfd=918&richsstsse