
Roku scored B (84%) with 221 issues across 7 tested pages, ranking #4 of 8 Testlio portfolio apps. That's 22 more than the 199.2 category average (38th percentile).
Top issues to fix immediately: "Critical: Resource failed to load (HTTP 404) breaking UI assets" — Identify the missing asset URL from the network panel, verify the file exists at the expected path on the server and ...; "Critical: DNS resolution failure blocks resource loading (ERR_NAME_NOT" — Audit all external hostnames used by the app, verify DNS records are correct and reachable from client environments, ...; "Non-descriptive alt text on informative image (alt='S')" — Replace the alt text with a concise, descriptive description of the image content (e.
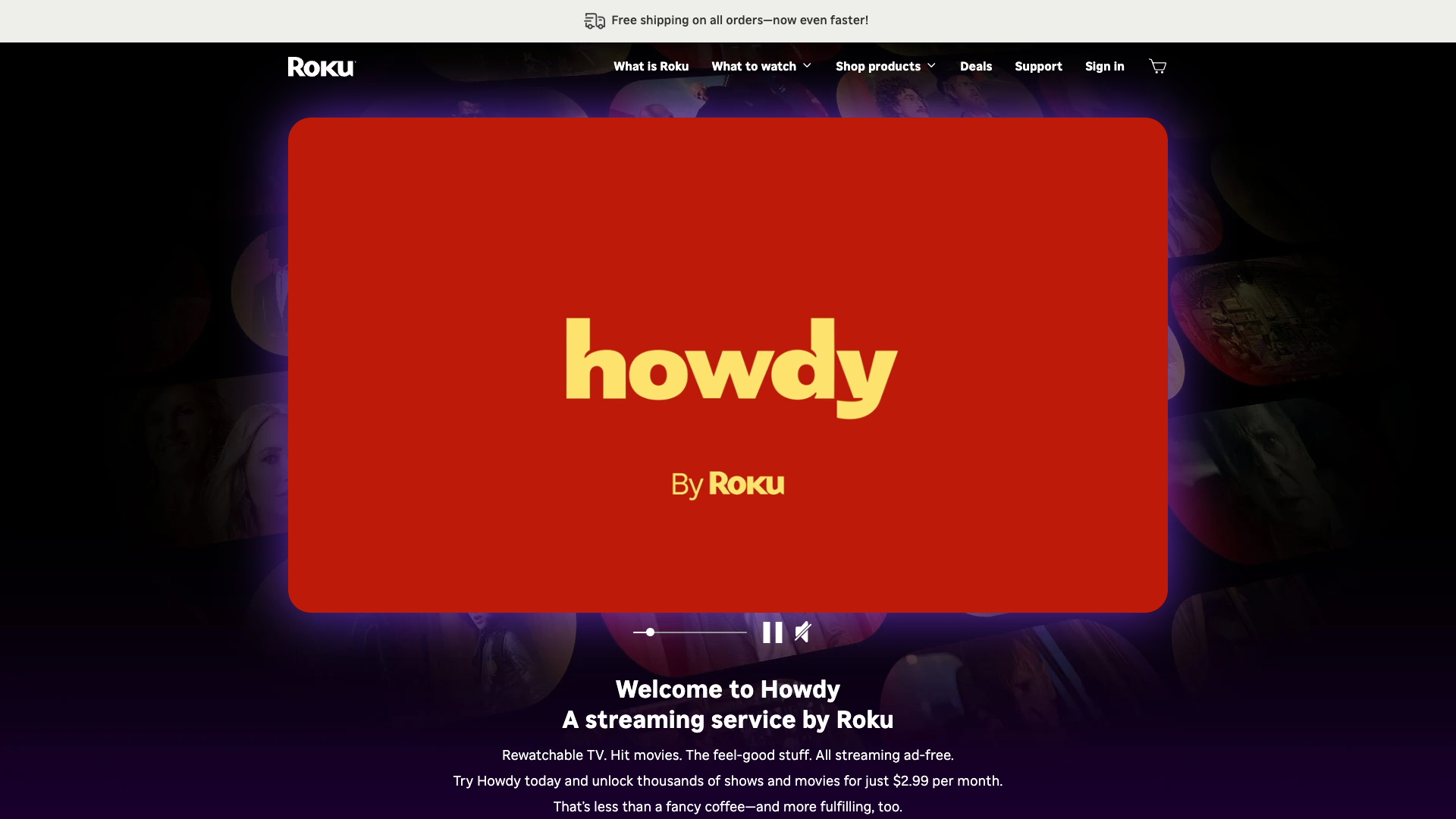
Weakest area — usability (6/10): Intuitive concept but navigation depth and the amount of content on a long scroll may hinder quick task completion.
Quick wins: Simplify the top navigation and add a prominent search and sign-in path to reduce cognitive load on first visit. Improve accessibility: provide clear focus indicators, scalable fonts, alt text for media, and skip-to-content links.

 Sharon · Security Networking Analyzer
Sharon · Security Networking AnalyzerGET https://pixel.web.roku.com/api/v2/scribe?app=www&eventType=action&uvn=undefined&usn=undefined&ip=24.17.117.100&experiment=RRuYXG9UN%7CRRuYXG9UN%232%2CK4Vhc3QXy%7CK4Vhc3QXy%23Test%2CCIxKUTHXP%7CCIxKUTHXP%232%2CoHxxc92JA%7CoHxxc92JA%231%2C1OOOoAe5Z%7C1OOOoAe5Z%231%2CzAdA8cu8K%7CzAdA8cu8K%231&auth=undefined&locale=%7B%22country%22%3A%22undefined%22%2C%22language%22%3A%22undefined%22%7D&channelStoreCode=US×tamp=1773791686358&action=Pageview&page=https%3A%2F%2Fwww.roku.com%2Fcheckout&referrer=&devices=%5B%7B%7D%5D& Jason · GenAI Code Analyzer
Jason · GenAI Code AnalyzerPOST https://www.google.com/ccm/collect?frm=0&ae=g&en=page_view...&ip=24.17.117.100&...POST https://pixel.web.roku.com/api/v2/scribe?app=www&eventType=action&uvn=undefined&usn=undefined&ip=24.17.117.100&experiment=RRuYXG9UN%7CRRuYXG9UN%232%2CK4Vhc3QXy%7CK4Vhc3QXy%23Test%2CCIxKUTHXP%7CCIxKUTHXP%232%2CoHxxc92JA%7CoHxxc92JA%231%2C1OOOoAe5Z%7C1OOOoAe5Z%231%2CzAdA8cu8K%7CzAdA8cu8K%231&auth=undefined&locale=%7B%22country%22%3A%22undefined%22%2C%22language%22%3A%22undefined%22%7D&channelStoreCode=US×tamp=1773791686358&action=Pageview&page=https%3A%2F%2Fwww.roku.com%2Fcheckout&referrer=&devices=%5B%7B%7D%5D& Jason · GenAI Code Analyzer
Jason · GenAI Code AnalyzerGET https://pixel.web.roku.com/api/v2/scribe?app=www&eventType=action&uvn=12702698-97e0-4322-b20e-fe2f4046c962%3Ad1f8bb969dcd581fa33634b57b508708&usn=false&ip=24.17.117.100&experiment=&auth=false&locale=%7B%22country%22%3A%22US%22%2C%22language%22%3A%22en%22%7D&channelStoreCode=US×tamp=1773791704939&action=Pageview&page=https%3A%2F%2Fwww.roku.com%2Fwhats-on&referrer=&devices=%5B%7B%7D%5D&misc=%7B%22utmcsr%22%3A%22(direct)%22%2C%22utmcmd%22%3A%22(none)%22%2C%22utmccn%22%3A%22(not%20set)%22%7D&GET https://pixel.web.roku.com/api/v2/scribe?app=www&eventType=action&uvn=12702698-97e0-4322-b20e-fe2f4046c962%3Ad1f8bb969dcd581fa33634b57b508708&usn=false&ip=24.17.117.100&experiment=&auth=false&locale=%7B%22country%22%3A%22US%22%2C%22language%22%3A%22en%22%7D&channelStoreCode=US×tamp=1773791704939&action=Pageview&page=https%3A%2F%2Fwww.roku.com%2Fwhats-on&referrer=&devices=%5B%7B%7D%5D&misc=%7B%22utmcsr%22%3A%22(direct)%22%2C%22utmcmd%22%3A%22(none)%22%2C%22utmccn%22%3A%22(not%20set)%22%7D&