
Netflix scored B+ (89%) with 117 issues across 7 tested pages, ranking #1 of 8 Testlio portfolio apps. That's 82 fewer than the 199.2 category average (88th percentile).
Top issues to fix immediately: "Promo/cookie banner obstructs the main hero and CTA" — Make the banner non-blocking for the initial view: move it to a non-overlapping area (e; "Critical: DNS resolution failures causing asset loads to fail (ERR_NAM" — Audit all asset hostnames used by the app (scripts, styles, images, fonts); "AdTech iframe data payload leaks membership and location details to th" — Minimize data shared with third parties by removing raw membership/location attributes from the URL.
Weakest area — accessibility (6/10): High-contrast colors help readability, but busy hero and image-heavy content may challenge screen readers and keyboard users; n...
Quick wins: Increase hero readability with a subtler overlay or simplified background to improve text contrast. Add a prominent, accessible search bar and skip links for keyboard users.






 Pete · Privacy Networking Analyzer
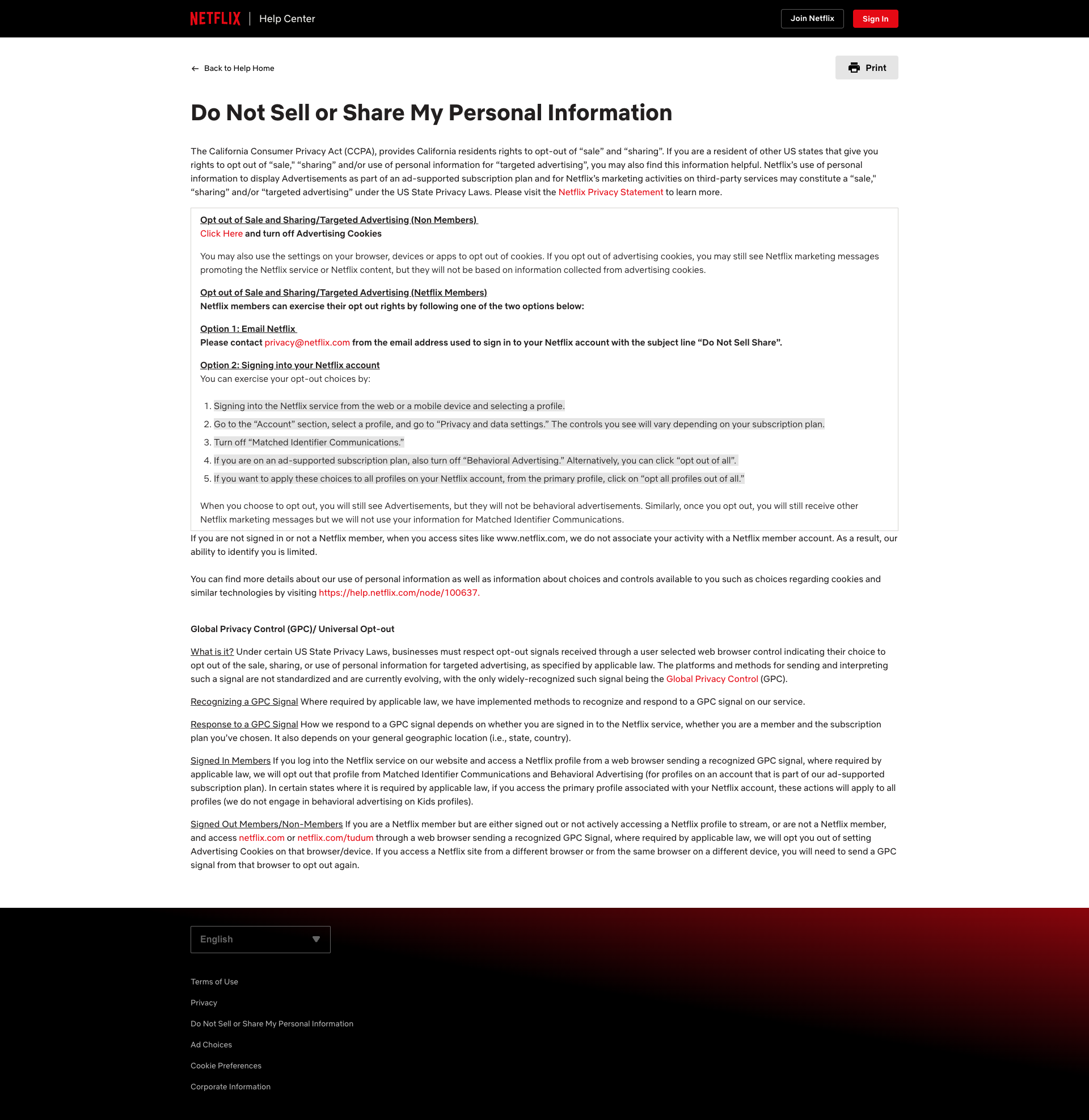
Pete · Privacy Networking AnalyzerGET https://ae.nflximg.net/monet/scripts/adtech_iframe_target_05.html?data=%7B%22membership_status%22%3A%22ANONYMOUS%22%2C%22country%22%3A%22US%22%2C%22region_code%22%3A%22WA%22%2C%22is_member%22%3A%22ANONYMOUS%22%2C%22wasFormerMember%22%3Afalse%2C%22referrer%22%3A%22nmLanding%22%2C%22deniedConsentCookieGroups%22%3A%22C0005%22%7D - Status: N/AGET https://ae.nflximg.net/monet/scripts/adtech_iframe_target_05.html?data=%7B%22membership_status%22%3A%22ANONYMOUS%22%2C%22country%22%3A%22US%22%2C%22region_code%22%3A%22WA%22%2C%22is_member%22%3A%22ANONYMOUS%22%2C%22wasFormerMember%22%3Afalse%2C%22referrer%22%3A%22nmLanding%22%2C%22deniedConsentCookieGroups%22%3A%22C0005%22%7D - Status: N/A Jason · GenAI Code Analyzer
Jason · GenAI Code Analyzer⚠️ AI/LLM ENDPOINT DETECTEDDetected AI endpoint calls logged by console; exact endpoints not shown in screenshot, but the messages indicate AI-related network activity. Pete · Privacy Networking Analyzer
Pete · Privacy Networking AnalyzerGET https://geolocation.onetrust.com/cookieconsentpub/v1/geo/location - Status: N/AGET https://geolocation.onetrust.com/cookieconsentpub/v1/geo/location - Status: N/A