
Jacamo scored B (83%) with 131 issues across 7 tested pages, ranking #8 of 14 US retail sites. That's 26 more than the 105.1 category average (36th percentile).
Top issues to fix immediately: "Access Denied Page Blocks User from Completing Task" — Display a user-friendly error message that explains why access was denied (e; "Critical: 403 Access Denied Error Blocks Page Load" — Investigate the 403 Forbidden error on the server; "Missing Cache Headers on All Critical Resources" — 1) Add Cache-Control headers to all responses: use 'max-age=31536000, immutable' for versioned assets in _next/static....
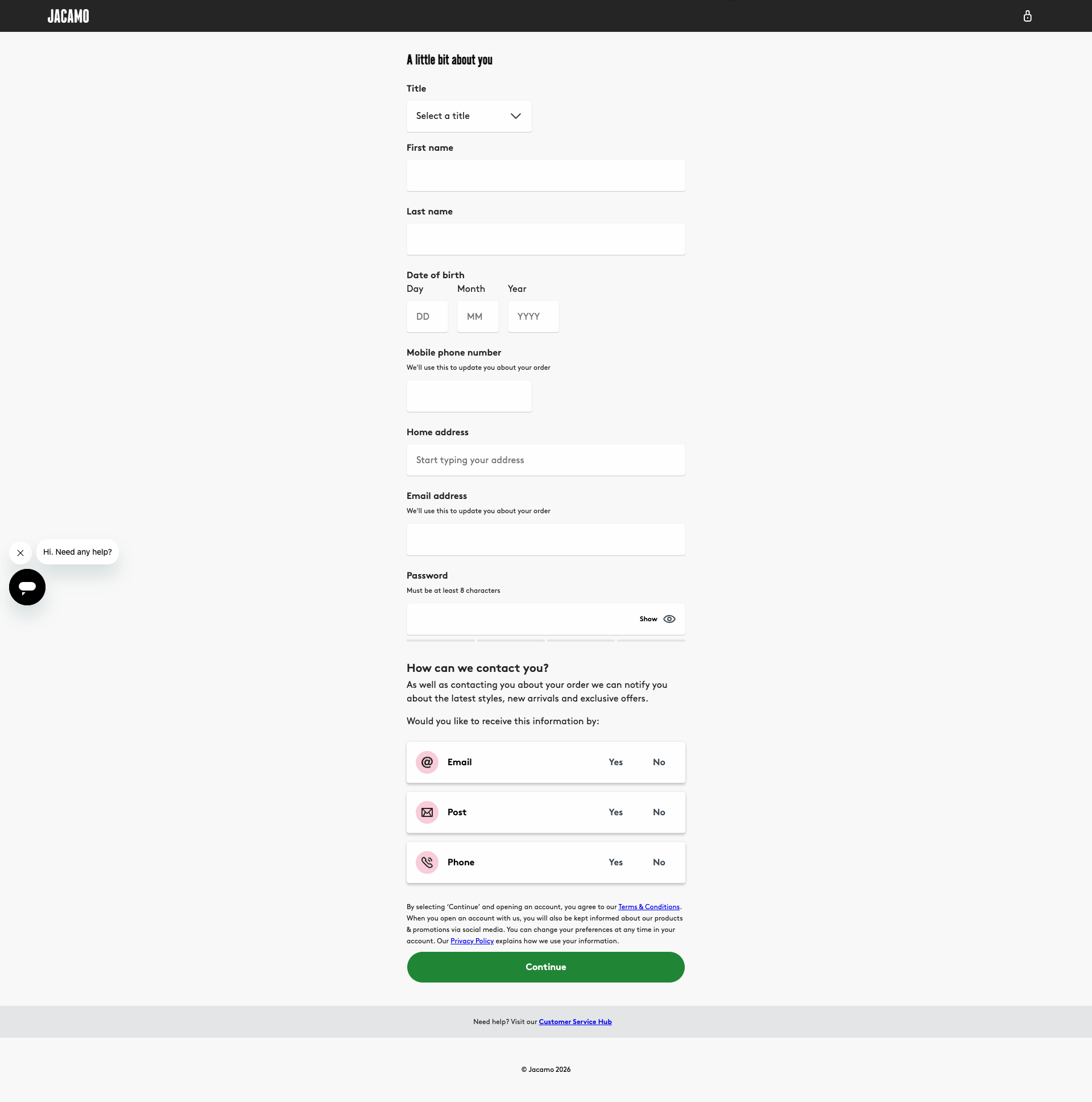
Weakest area — accessibility (5/10): Significant concerns with color contrast ratios, no visible alt text strategy, and potential keyboard navigation issues.
Quick wins: Improve color contrast ratios, especially red text on dark backgrounds, to meet WCAG AA standards. Add descriptive alt text to all product images and banner graphics.




 Sharon · Security Tester
Sharon · Security Tester[ERROR] Framing 'https://sgtm.jacamo.co.uk/' violates the following Content Security Policy directive: "frame-src 'self' https://fp.simplybe.co.uk https://fp.jdwilliams.co.uk https://fp.jacamo.co.uk https://h.online-metrix.net". The request has been blocked.Frame loading attempt blocked by CSP Jason · GenAI Code Analyzer
Jason · GenAI Code Analyzer[ERROR] Framing 'https://sgtm.jacamo.co.uk/' violates the following Content Security Policy directive: "frame-src 'self' https://fp.simplybe.co.uk https://fp.jdwilliams.co.uk https://fp.jacamo.co.uk https://h.online-metrix.net". The request has been blocked. [WARN] Failed to execute 'postMessage' on 'DOMWindow': The target origin provided ('https://sgtm.jacamo.co.uk') does not match the recipient window's origin ('null').GET https://sgtm.jacamo.co.uk/gtm.js?id=GTM-K56QNZLS - Status: 200 (but blocked by CSP at frame level) Jason · GenAI Code Analyzer
Jason · GenAI Code Analyzer[ERROR] Framing 'https://sgtm.jacamo.co.uk/' violates the following Content Security Policy directive: "frame-src 'self' https://fp.simplybe.co.uk https://fp.jdwilliams.co.uk https://fp.jacamo.co.uk https://h.online-metrix.net". The request has been blocked.GET https://sgtm.jacamo.co.uk/gtm.js?id=GTM-K56QNZLS - Status: 200