
Culture Kings scored B (84%) with 121 issues across 6 tested pages, ranking #7 of 14 US retail sites. That's 16 more than the 105.1 category average (50th percentile).
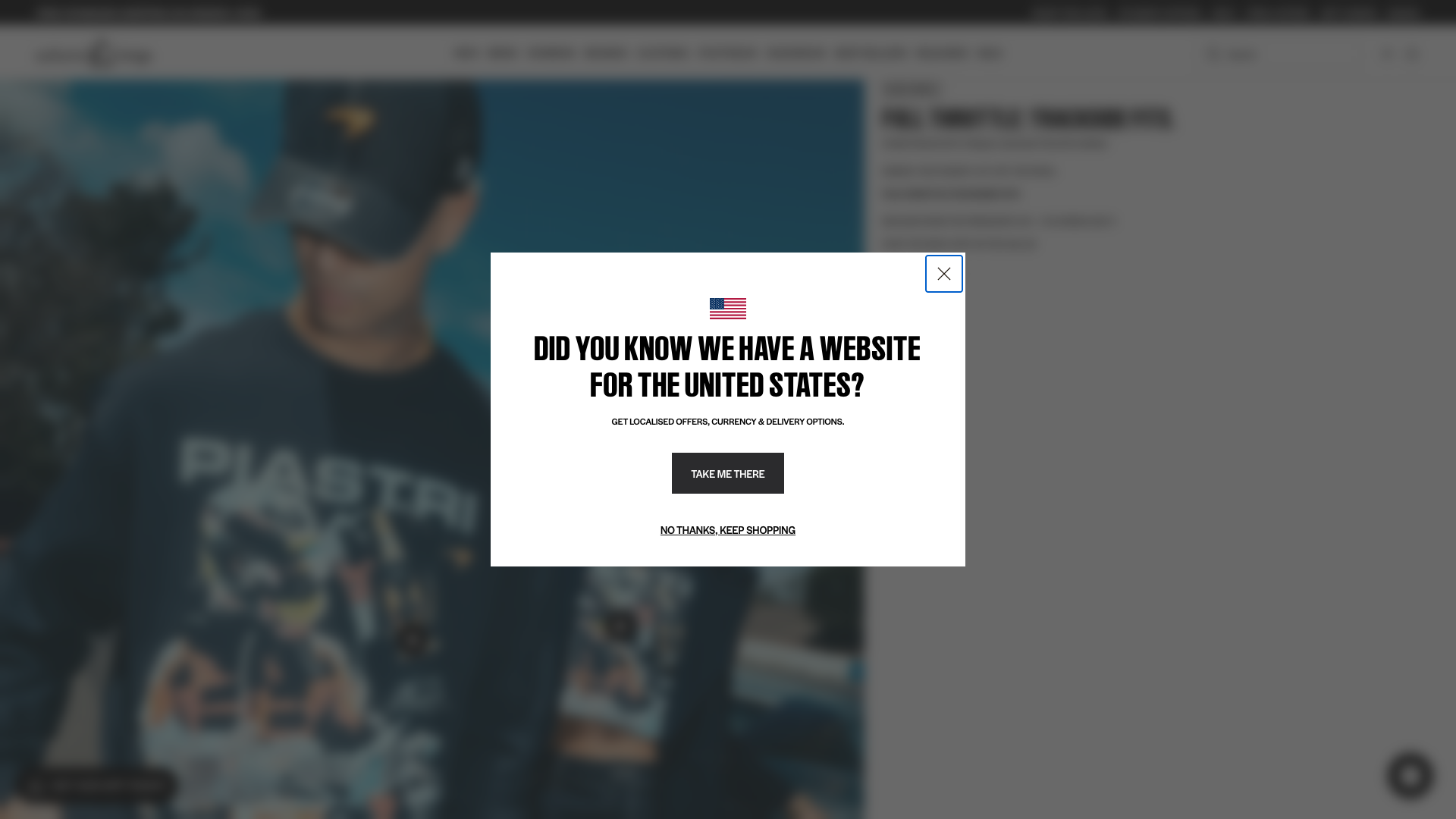
Top issues to fix immediately: "Modal Dialog Blocks Primary Content Without Clear Dismiss Mechanism" — Add a clearly visible close button (X icon) in the top-right corner of the modal dialog; "Multiple DNS resolution failures - ERR_NAME_NOT_RESOLVED" — 1) Identify which domains are failing to resolve by checking the Network tab in DevTools; "Multiple images with generic or missing alt text reduce accessibility " — Audit all images on the page and provide meaningful, descriptive alt text for informative images.
Weakest area — accessibility (5/10): Significant accessibility issues including low contrast text on dark backgrounds, unclear alt text for product images, and navi...
Quick wins: Improve color contrast ratios throughout the site to meet WCAG AA standards, especially for body text on dark.... Add descriptive alt text to all product images and ensure semantic HTML structure for screen readers.



 Jason · GenAI Code Analyzer
Jason · GenAI Code Analyzer[LOG] [FloatingWidget] continue legacy widget flowGET https://edge.personalizer.io/storefront/2.0.0/js/shopify/storefront.min.js - Status: 200 (fires on initial page load), POST https://monorail-edge.shopifysvc.com/unstable/produce_batch - Status: N/A Sharon · Security Networking Analyzer
Sharon · Security Networking AnalyzerGET https://edge.personalizer.io/storefront/2.0.0/js/shopify/storefront.min.js?key=bpybl-z2aht7u5glt8snw4jkw-ojruj&shop=culture-kings-2.myshopify.com Sharon · Security Networking Analyzer
Sharon · Security Networking AnalyzerNetwork request showing query parameter exposureGET https://edge.personalizer.io/storefront/2.0.0/js/shopify/storefront.min.js?key=bpybl-z2aht7u5glt8snw4jkw-ojruj&shop=culture-kings-2.myshopify.com