
Asda scored B (84%) with 149 issues across 6 tested pages, ranking #17 of 20 UK retail sites. That's 19 more than the 130.2 category average (20th percentile).
Top issues to fix immediately: "Content Security Policy Misconfiguration - script-src 'none' with Repo" — (1) Change CSP from report-only to enforcing mode (remove 'report-only'); "Content Security Policy Completely Disabled - script-src 'none' with R" — 1; "Content Security Policy Misconfiguration - All Scripts Blocked Due to " — Immediately audit and fix the CSP header configuration.
Weakest area — accessibility (5/10): Limited visible accessibility features. Color contrast appears adequate but alt text, ARIA labels, and screen reader optimizati...
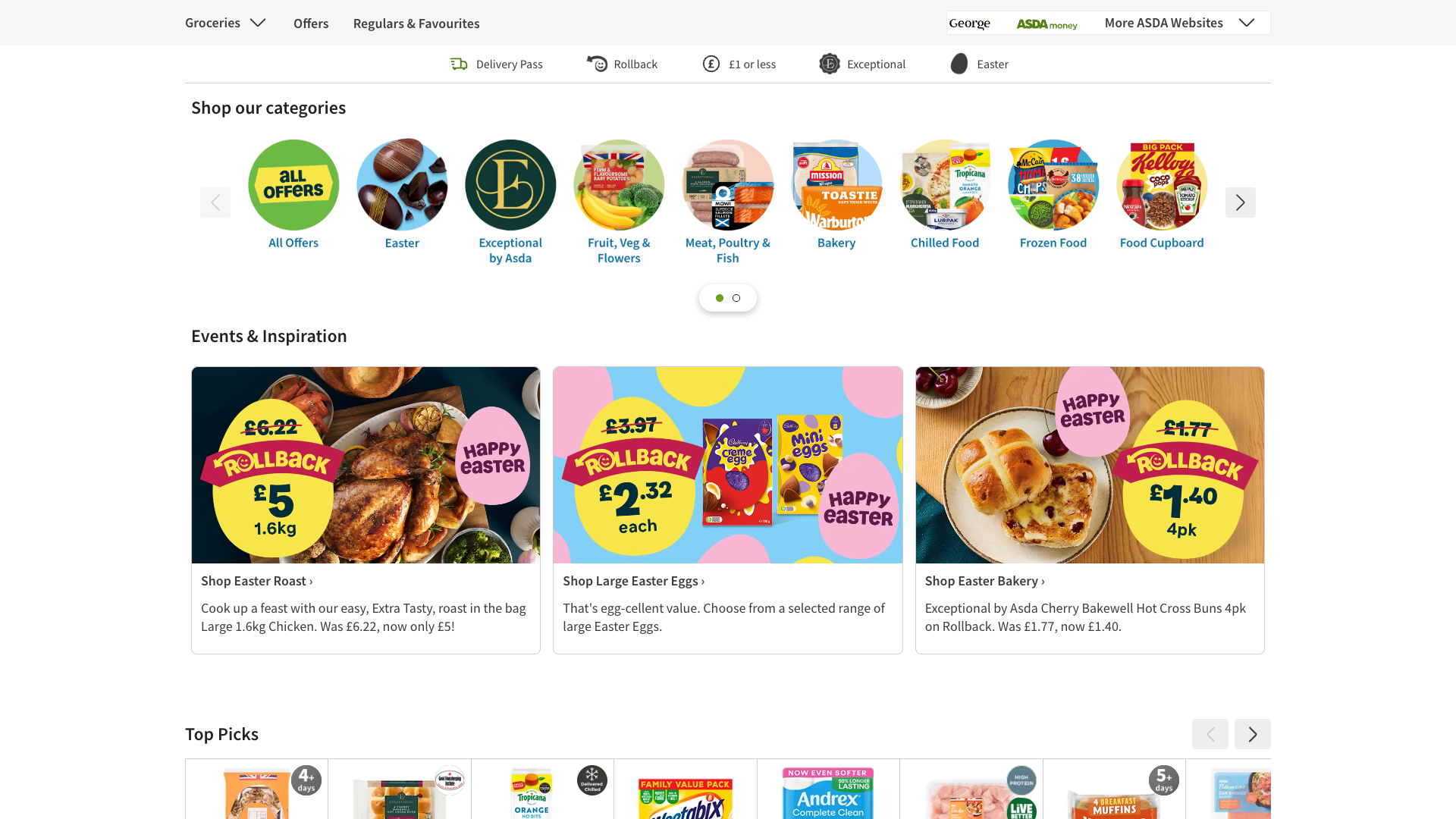
Quick wins: Enhance accessibility by implementing clear skip navigation links and ensuring ARIA labels are properly applied. Add more descriptive text to promotional banners explaining offers and benefits clearly.

 Sharon · Security Console Log Analyzer
Sharon · Security Console Log Analyzer[INFO] Loading the script 'https://cdn-ukwest.onetrust.com/scripttemplates/otSDKStub.js' violates the following Content Security Policy directive: "script-src 'none'". The policy is report-only, so the violation has been logged but no further action has been taken.Multiple script loading violations: OneTrust, Google Tag Manager (GTM-MJ2VMHG), Dynamic Yield, Medallia, Adobe DTM, Cloudflare Insights Sharon · Security Console Log Analyzer
Sharon · Security Console Log Analyzer[INFO] Loading the script 'https://cdn-ukwest.onetrust.com/scripttemplates/otSDKStub.js' violates the following Content Security Policy directive: "script-src 'none'". Note that 'script-src-elem' was not explicitly set, so 'script-src' is used as a fallback. The policy is report-only, so the violation has been logged but no further action has been taken. [INFO] Loading the script 'https://www.googletagmanager.com/gtm.js?id=GTM-MJ2VMHG' violates the following Content Security Policy directive: "script-src 'none'". [INFO] Executing inline script violates the following Content Security Policy directive 'script-src 'none''.Multiple script loading violations from external domains (OneTrust, Google Tag Manager, Medallia, Dynamic Yield, Adobe Launch, Cloudflare, etc.) all proceeding despite CSP violations. Jason · GenAI Code Analyzer
Jason · GenAI Code Analyzer[ERROR] Fetch API cannot load https://cdn-eu.dynamicyield.com/scripts/2.80.0/dy-coll-nojq-min.js. Refused to connect because it violates the document's Content Security Policy.GET https://cdn-eu.dynamicyield.com/scripts/2.80.0/dy-coll-nojq-min.js - BLOCKED by CSP