B85%
Quality Score
7
Pages
105
Issues
8.0
Avg Confidence
7.8
Avg Priority
48 Critical36 High21 Medium

>_ Testers.AI
AI Analysis
Nxcode was tested and 105 issues were detected across the site. The most critical finding was: Unconsented loading of third-party analytics tracking scripts on page load. Issues span Security, Legal, A11y, Performance categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (7/10).
Qualitative Quality
Nxcode
Category Avg
Best in Category
Pages Tested · 7 screenshots
Homepage
www.nxcode.io
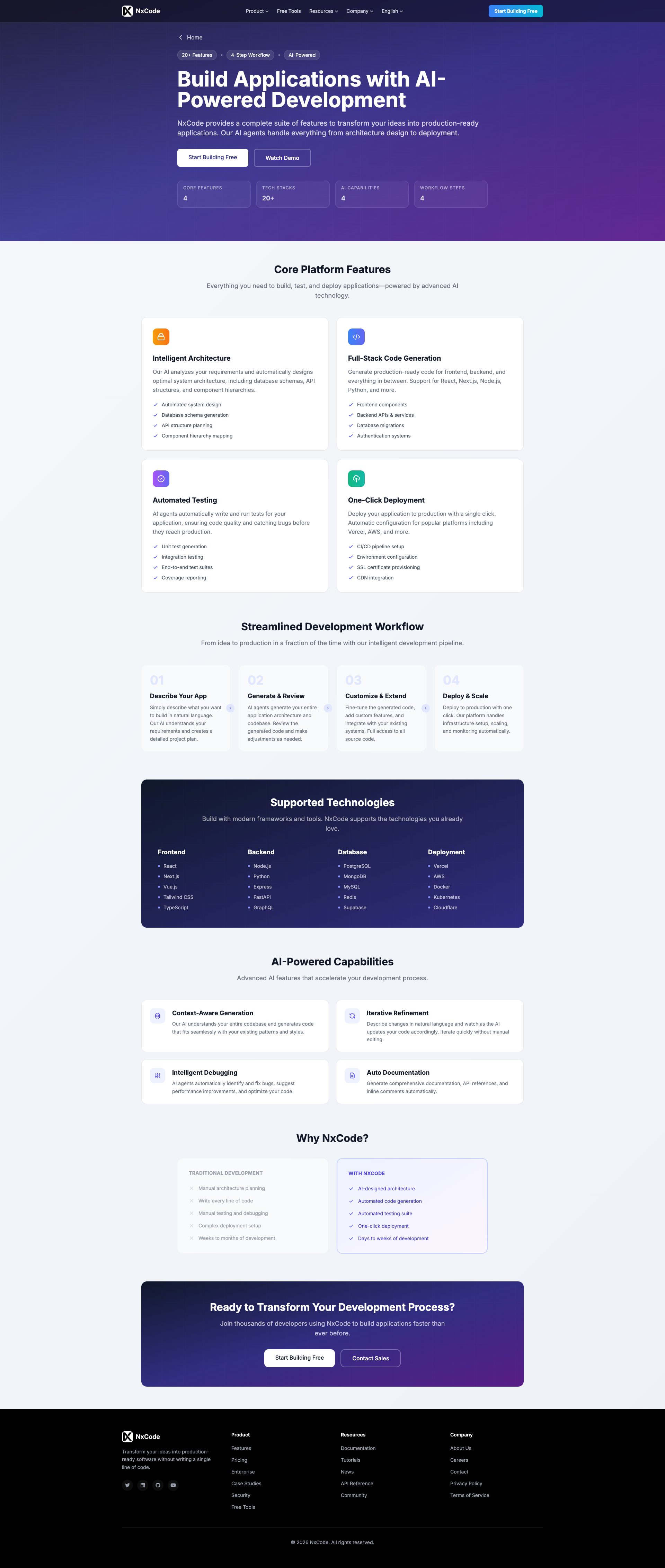
www.nxcode.io
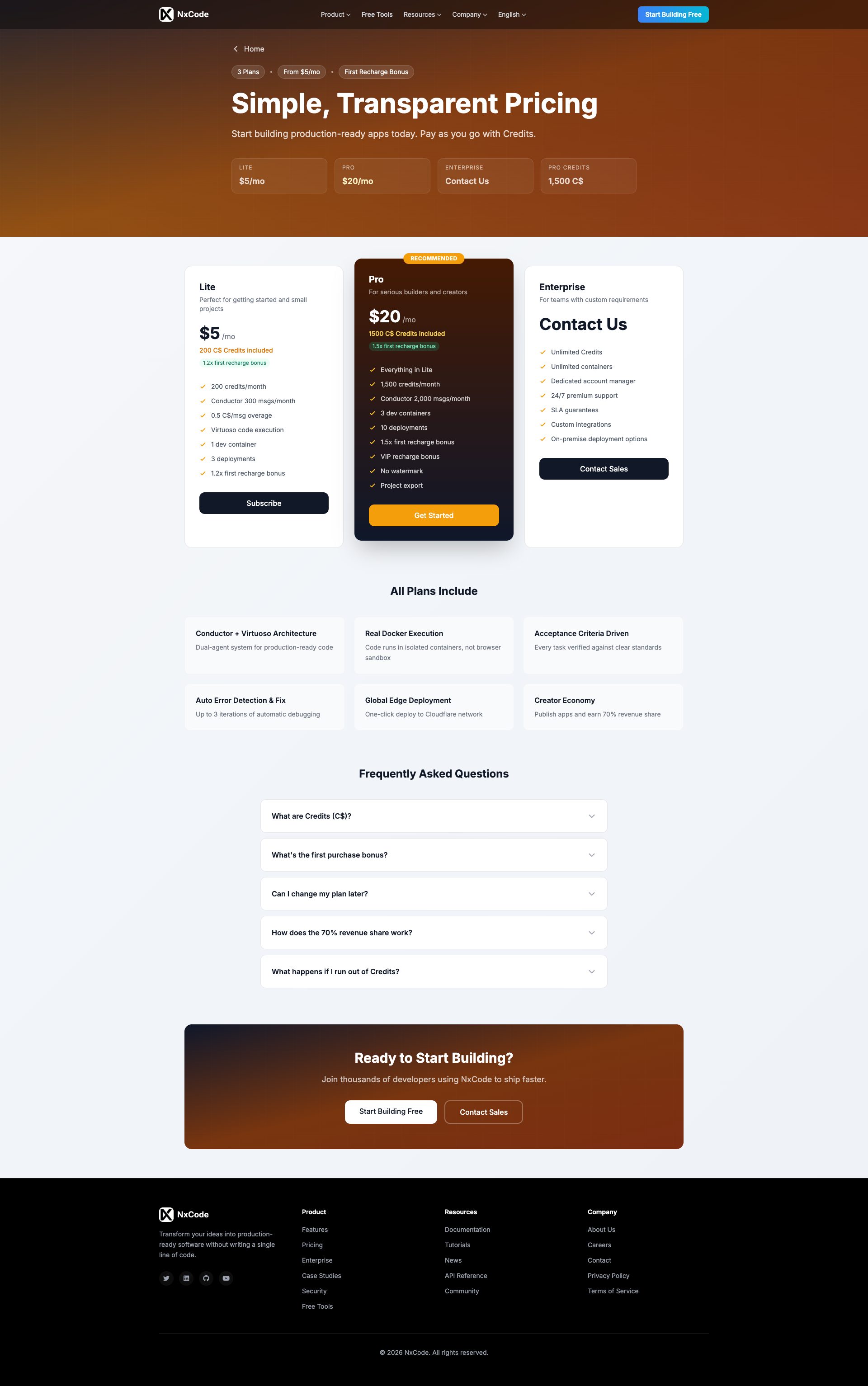
www.nxcode.io
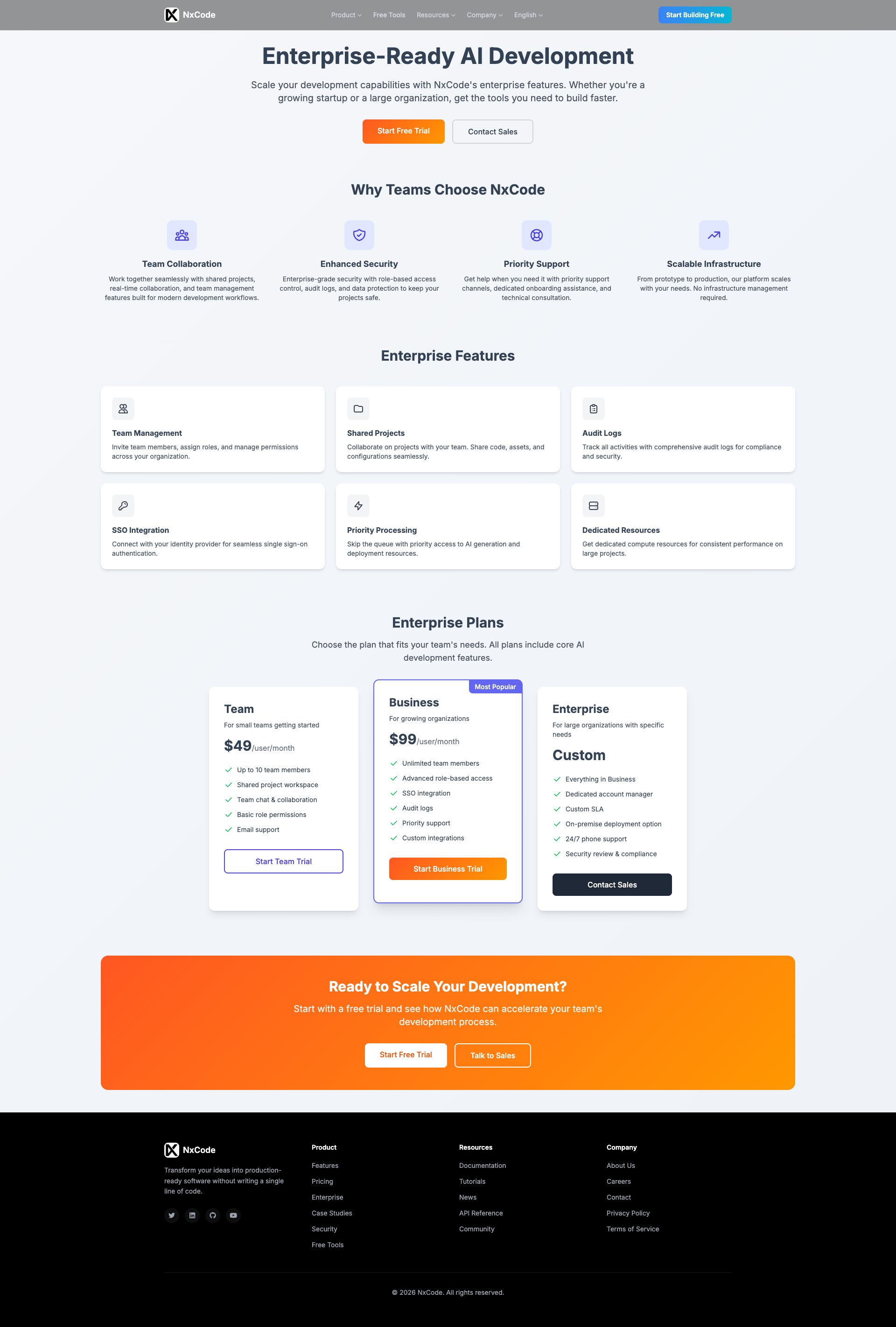
www.nxcode.io
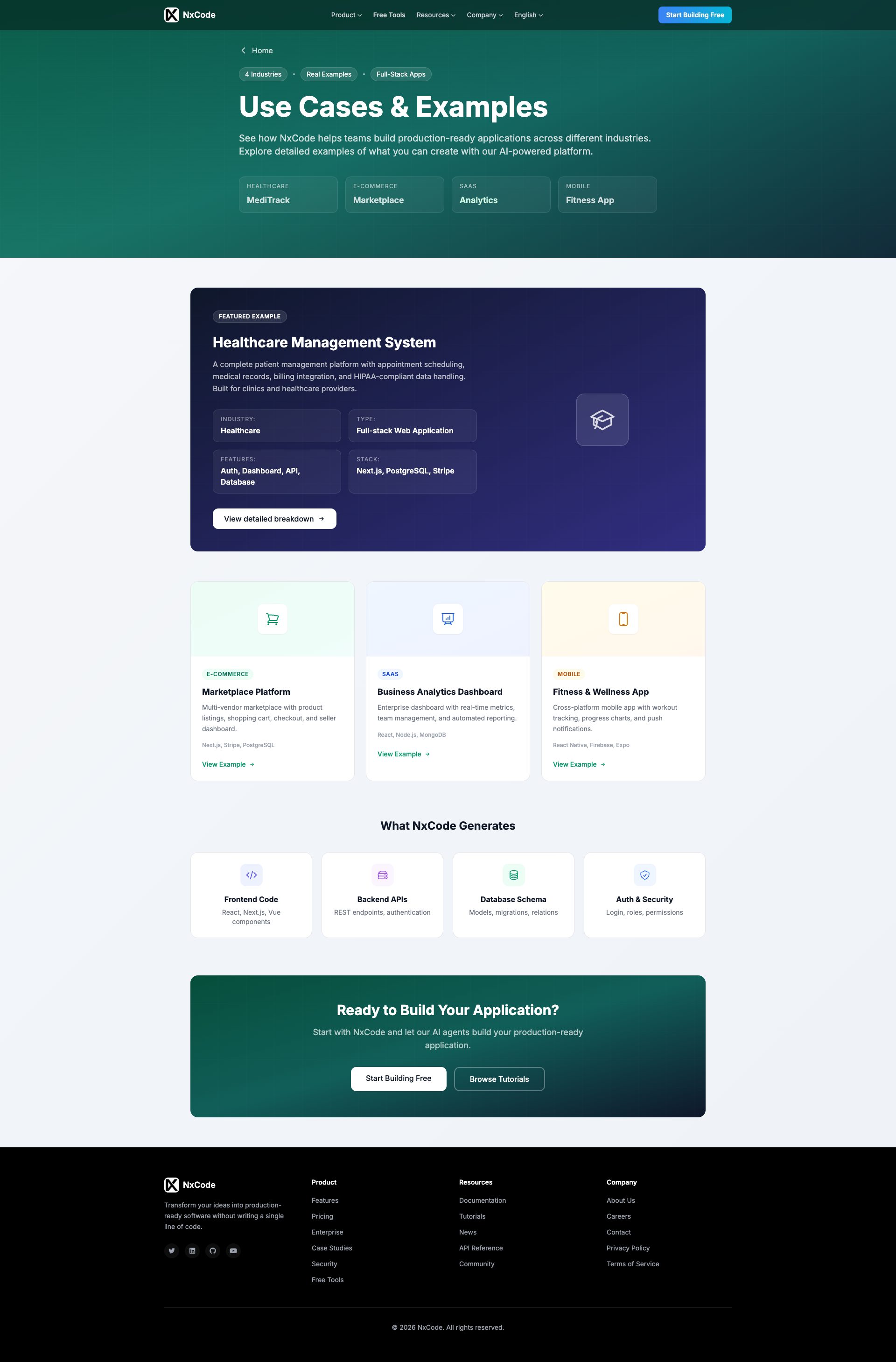
www.nxcode.io
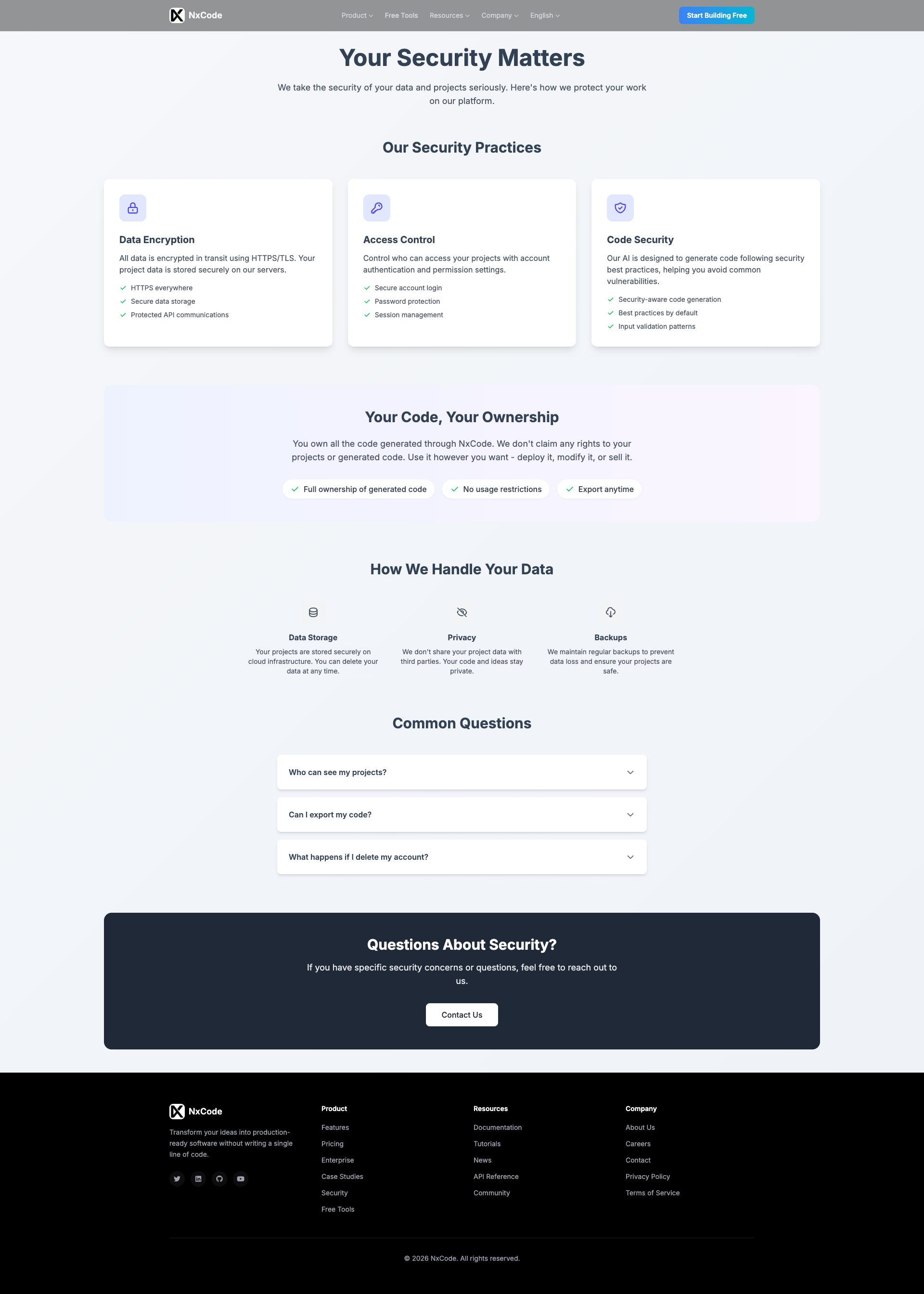
www.nxcode.io
Detected Issues · 105 total
1
Unconsented loading of third-party analytics tracking scripts on page load
CRIT P9
Prompt to Fix
Add a consent gating mechanism before loading any third-party analytics scripts. Wrap every analytics script load behind a consent check; if consent not given, do not load the script. After consent, initialize GA4 with anonymized IPs, disable ad personalization, and avoid sending personally identifiable information. Update CSP to block third-party analytics by default and provide a clear privacy/cookie banner explaining data collection.
Why it's a bug
Page requests load multiple third-party analytics/tracking scripts (Google Analytics via gtag.js, Microsoft Clarity, Cloudflare Insights beacon) with no evident consent gating in the captured activity, enabling automatic user activity tracking and potential cross-site profiling without user permission.
Why it might not be a bug
Consent mechanisms may exist elsewhere (e.g., a CMP banner not captured in this log). However, the provided network activity shows analytics scripts loading without clear consent gating in the trace, indicating a privacy risk absent explicit consent.
Suggested Fix
Integrate a Consent Management Platform (CMP) and gate all analytics scriptsbehind user consent. Delay loading of gtag.js, Clarity, and Cloudflare beacon until consent is given. Implement IP anonymization and reduced data collection for analytics (disable ad personalization, set appropriate data retention). Enforce a strict Content Security Policy to block third-party analytics until consent is granted.
Why Fix
Ensures compliance with privacy regulations (e.g., GDPR/CCPA), reduces unconsented data collection, and improves user trust by aligning tracking with user consent preferences.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
https://www.googletagmanager.com/gtag/js?id=G-4SRCM9DPMY; https://static.cloudflareinsights.com/beacon.min.js/v8c78df7c7c0f484497ecbca7046644da1771523124516; https://www.clarity.ms/tag/ufthalijxz2
Exposed internal Page Content data (debug JSON) in UI
CRIT P9
Prompt to Fix
Remove or hide the serialized Page Content JSON block from the UI. If debugging data is needed for development, gate it behind a feature flag or separate debug route not exposed in production.
Why it's a bug
The UI displays a raw Page Content JSON structure (buttons, links, etc.). This is internal debugging data and code structure leaking to end users, creating a security/privacy risk and making the page brittle to changes.
Why it might not be a bug
If this JSON was meant for developer preview only, it should not be rendered in production UI. In production builds, this data should be removed or gated behind a developer flag.
Suggested Fix
Remove the 'Page Content' debug block from production. Ensure only safe, presentation-friendly data is rendered. If needed for dynamic content, fetch securely and sanitize before rendering.
Why Fix
Reduces attack surface, prevents exposure of internal data structures, and improves production security and user experience.
Route To
Frontend/Full-stack Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
Page Content: {"buttons":[{"text":"Product","tagName":"BUTTON","type":"submit","id":""...}]}3
AI/LLM endpoint calls detected on page load (privacy/performance risk)
CRIT P9
Prompt to Fix
Audit production code for any immediate on-load calls to AI/LLM endpoints or instrumentation. Remove or gate these calls (and corresponding console logs) behind a feature flag. If LLM interactions are required, load them only after user interaction or explicit consent and ensure logs do not reveal endpoint details in production.
Why it's a bug
Console logs show '⚠️ AI/LLM ENDPOINT DETECTED' during initial page render, indicating AI-endpoint calls or instrumentation fire on load. This can leak data, slow down startup, and reveal internal tooling to users.
Why it might not be a bug
If the detections are strictly debug instrumentation intended for development builds, they could be gated behind a feature flag or removed in production.
Suggested Fix
Remove on-load AI endpoint calls/logs from production code or guard them behind a feature flag; lazy-load any LLM interactions behind user action or explicit consent; ensure production builds do not emit AI-endpoint logs.
Why Fix
Prevents potential data leakage, reduces network overhead on first paint, and improves user trust and perceived performance.
Route To
Frontend Engineer / Platform Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
N/A - console log indicates detection, not a direct network request shown in snippet