C+79%
Quality Score
7
Pages
132
Issues
8.0
Avg Confidence
7.9
Avg Priority
52 Critical62 High18 Medium

>_ Testers.AI
AI Analysis
Ipshopy was tested and 132 issues were detected across the site. The most critical finding was: Exposure of Meta Pixel tracking IDs in console logs. Issues span Security, Performance, A11y, Other categories. Persona feedback rated Visual highest (6/10) and Accessibility lowest (4/10).
Qualitative Quality
Ipshopy
Category Avg
Best in Category
Pages Tested · 7 screenshots

Homepage
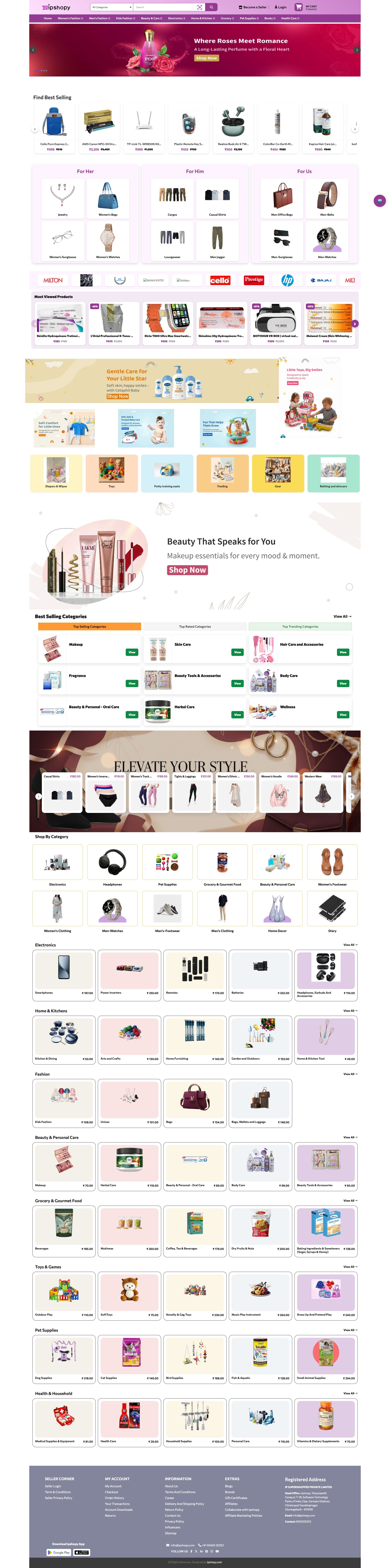
www.ipshopy.com
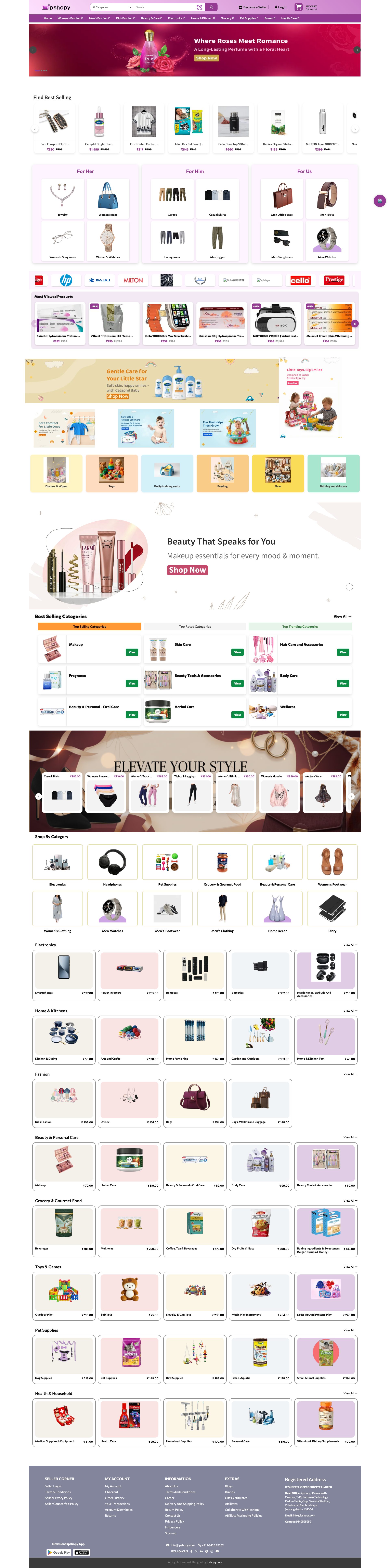
www.ipshopy.com

www.ipshopy.com
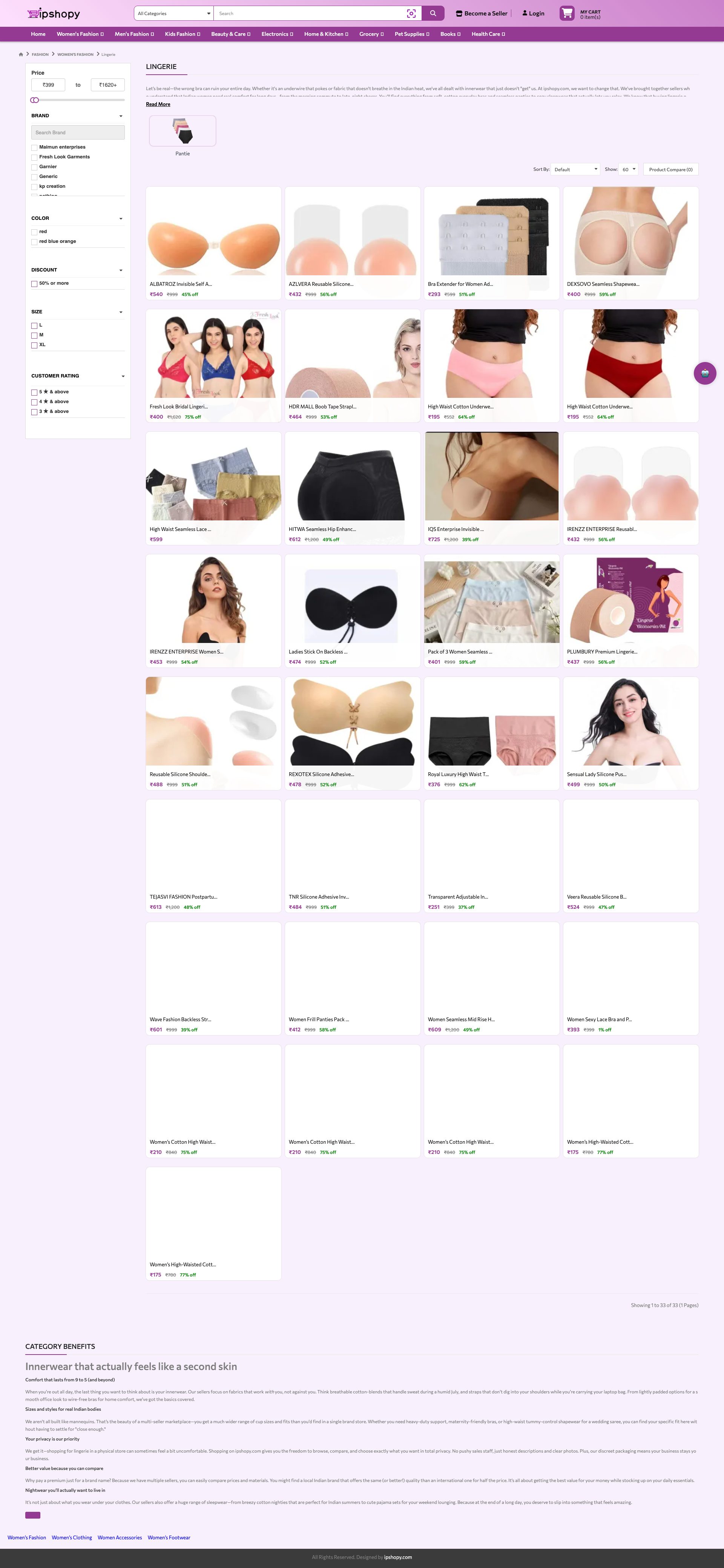
www.ipshopy.com

www.ipshopy.com
www.ipshopy.com
Detected Issues · 132 total
1
Exposure of Meta Pixel tracking IDs in console logs
CRIT P9
Prompt to Fix
Audit all client-side console logs for analytics/tracking identifiers. Remove logging of Meta Pixel IDs or redact them (e.g., 'PixelID_REDACTED'). Ensure analytics scripts do not print IDs to console. Wrap such logs in a development-only flag or remove entirely from production builds. If debugging is needed, replace IDs with non-identifying placeholders and sanitize network calls.
Why it's a bug
Console logs reveal Meta Pixel IDs (e.g., 1847743629127484, 854612657635027), which are tracking identifiers used by third parties. Printing these IDs in the client console can enable cross-site tracking or profiling by unintended actors and increases the risk of data leakage.
Why it might not be a bug
While debugging, developers may log identifiers; however, exposing third-party tracking IDs in production console logs constitutes a privacy risk and should be avoided regardless of debugging needs.
Suggested Fix
Remove or redact Meta Pixel IDs from all console logs. Gate analytics-related logs behind a development-only flag or environment check. Implement a redaction function to mask IDs (e.g., PixelID_REDACTED) and ensure logs do not reveal tracking identifiers. Consider moving such logging to server-side telemetry with proper data governance.
Why Fix
Preventing exposure of third-party tracking identifiers in client-side logs reduces the risk of cross-site tracking, preserves user privacy, and improves compliance with privacy regulations.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Console Log Analyzer
Technical Evidence
Console:
[WARN] [Meta Pixel] - Duplicate Pixel ID: 1847743629127484.
[WARN] [Meta Pixel] - Duplicate Pixel ID: 854612657635027.2
PII exposure in image URL path (user name in file path)
CRIT P9
Prompt to Fix
Replace asset file paths that contain personal names with opaque IDs. On upload, sanitize filenames and store mapping in DB. Serve assets via URLs that do not expose original filenames or user names. Example: map 25001_... to a UUID-based path like /image/cache/catalog/asset/uuid-12345-180x180.webp, and ensure server-side logs and referer headers do not reveal the original filename.
Why it's a bug
Publicly accessible image URL contains a personal name within the path (Uploaded Data/Akash/...). This exposes Personally Identifiable Information (PII) in network requests and server logs, increasing risk of user identification and social engineering. Even if the name is a filename, it is still associated with a person and can be exposed via referer headers, server logs, or analytics.
Why it might not be a bug
If 'Akash' is an internal alias or the image is publicly uploaded without any sensitive PII, some teams may consider it non-sensitive. However, filenames containing real names are generally not acceptable as they can reveal personal information.
Suggested Fix
Do not expose user or staff real names in URLs. Store files with non-identifiable IDs (UUIDs) and maintain a server-side mapping. Generate CDN/asset URLs using opaque IDs or hash of content, not the original filename. Consider removing spaces and personal names from path. Sanitize and consolidate uploaded filenames.
Why Fix
Reduces exposure of PII in URLs, server logs, analytics, and Referer headers. Improves privacy by minimizing data in public asset paths.
Route To
Security/Platform Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
GET https://www.ipshopy.com/image/cache/catalog/Uploaded%20Data/Akash/25001_2025-09-02_09-04-02_607286_2025-09-02_10-58-13_873913_2025-11-05_09-04-31_541033_2025-11-05_09-06-39_484727_2025-12-17_09-22-36_223396-180x180.webp - Status: N/A3
Third-party tracking beacon loaded without clear consent
CRIT P9
Prompt to Fix
Remove or conditionally load Cloudflare's beacon.js behind a user consent check. If consent is granted, load with IP anonymization, disable collection of sensitive fields, and configure Cloudflare to respect Do Not Track and opt-out. Add a clear privacy notice about third-party analytics and a consent banner.
Why it's a bug
The site loads Cloudflare's beacon.js (static.cloudflareinsights.com/beacon.min.js), a third-party analytics/telemetry endpoint. This enables user activity tracking to a third party and may occur without explicit user consent, violating privacy expectations and potentially regulatory requirements.
Why it might not be a bug
Beacons are common for performance and security telemetry; however, without consent or explicit disclosure, this constitutes unconsented tracking. If consent mechanism exists elsewhere, this could be mitigated, but based on provided data, no consent prompt is visible.
Suggested Fix
Move third-party tracking behind a consent wall or disable until user opt-in. If needed, ensure IP anonymization and data minimization in requests to Cloudflare. Alternatively replace with first-party analytics or provide an opt-out.
Why Fix
Reduces cross-site tracking and data sharing with third parties, aligns with privacy regulations (GDPR/CCPA), and improves user trust.
Route To
Privacy/Frontend Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
GET https://static.cloudflareinsights.com/beacon.min.js/vcd15cbe7772f49c399c6a5babf22c1241717689176015 - Status: N/A