B86%
Quality Score
4
Pages
48
Issues
8.1
Avg Confidence
7.9
Avg Priority
21 Critical19 High8 Medium

>_ Testers.AI
AI Analysis
Attendflowio was tested and 48 issues were detected across the site. The most critical finding was: Unconsented third-party telemetry data sent to Sentry (privacy risk). Issues span Security, Legal, A11y, Performance categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (5/10).
Qualitative Quality
Attendflowio
Category Avg
Best in Category
Pages Tested · 4 screenshots
Homepage
lovable.dev.products.attendflowio
lovable.dev.products.attendflowio
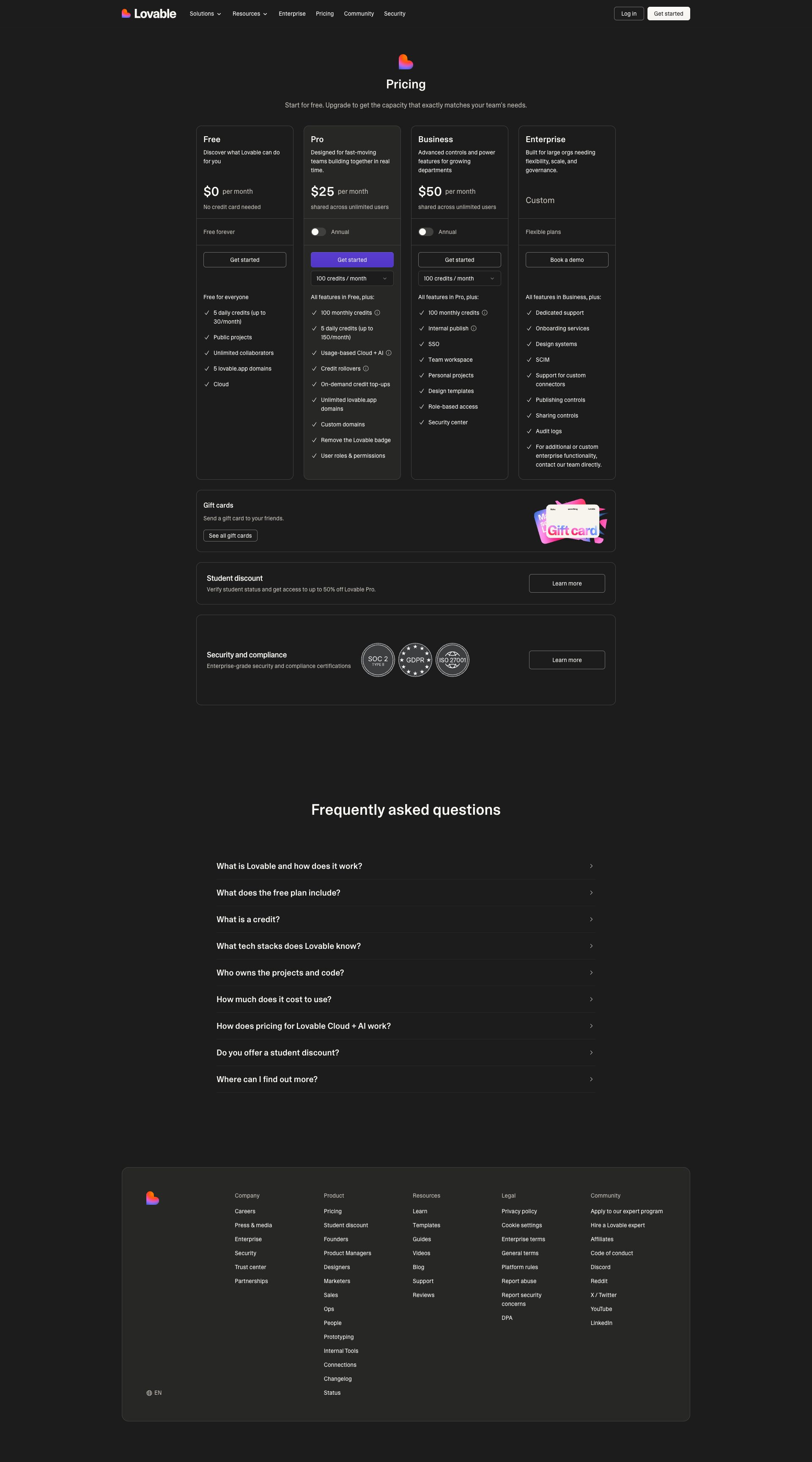
lovable.dev.products.attendflowio
Detected Issues · 48 total
1
Unconsented third-party telemetry data sent to Sentry (privacy risk)
CRIT P9
Prompt to Fix
In a Next.js app using Sentry for error tracking, implement explicit user consent for error telemetry and scrub any PII from events. Add a beforeSend hook to remove personal data (emails, usernames, user IDs), strip sensitive request headers (e.g., cookies), and enable anonymizeIp. Ensure sendDefaultPii is false and consider reducing data collection by lowering tracesSampleRate. Provide a visible privacy notice or consent toggle for telemetry.
Why it's a bug
A POST to Sentry's ingest API transmits telemetry data to a third-party service. The payload may include error details, user identifiers, or other data that could constitute PII. There is no evidence of an explicit user consent toggle or privacy notice visible in the observed network activity. This increases risk of data exposure and regulatory concerns.
Why it might not be a bug
Telemetry to Sentry is standard for error reporting; if explicit user consent is obtained and payloads are scrubbed, it could be acceptable. However, from the provided network activity, there is no visible consent indicator and the endpoint is a third party.
Suggested Fix
Implement privacy-preserving telemetry: disable or opt-out by default, or ensure explicit user consent for error reporting. Configure Sentry to scrub PII via beforeSend, minimize user context, avoid sending emails/user IDs, and strip cookies as needed. Enable IP anonymization (anonymizeIp) and data scrubbing rules. Ensure a clear privacy notice or consent control is presented to users.
Why Fix
Protects user privacy, reduces exposure of personal data to third parties, and aligns with data protection regulations and user trust.
Route To
Frontend/Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.0 - Status: N/A2
Credentials exposed in Sentry ingest URL (sentry_key in query string)
CRIT P9
Prompt to Fix
Replace the direct POST to the Sentry ingest endpoint with the official Sentry SDK in your Next.js app. Remove any query parameter containing sentry_key from the URL. Use the DSN-based configuration loaded from environment variables (e.g., SENTRY_DSN) and initialize Sentry with Sentry.init({ dsn: process.env.SENTRY_DSN, tracesSampleRate: 1.0 });. Do not construct ingestion URLs manually or expose keys in query strings. Ensure logs and error reports are sent through the SDK over HTTPS only and that no credentials appear in browser history, logs, or referer headers. Validate that no other credentials are sent in URLs.
Why it's a bug
The network log shows a POST to Sentry's ingest endpoint with authentication key sent as a query parameter (sentry_key) in the URL. Exposing API keys or credentials in URL query parameters can be logged in browser history, server logs, and referer headers, leading to credential leakage and potential misuse.
Why it might not be a bug
Some services intentionally put non-secret public keys in URLs for ingestion endpoints; however, even public keys can be exposed in logs. If this key is truly public and not sensitive, risk is lower, but best practices avoid exposing any credentials in URLs.
Suggested Fix
Migrate Sentry integration to use the official SDK with DSN-based authentication and avoid placing keys in the URL query. Remove the sentry_key parameter from the URL and ensure Sentry events are sent via TLS using environment-provided DSN. Do not log full URLs containing credentials. Consider using Sentry's Next.js SDK (@sentry/nextjs) and configure in environment as SENTRY_DSN.
Why Fix
Prevent credential leakage and reduce risk of credential exposure via logs, history, or referer headers. Align with security best practices to avoid secrets in URLs.
Route To
Security Engineer
Page
Tester
Sharon · Security Networking Analyzer
Technical Evidence
Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.03
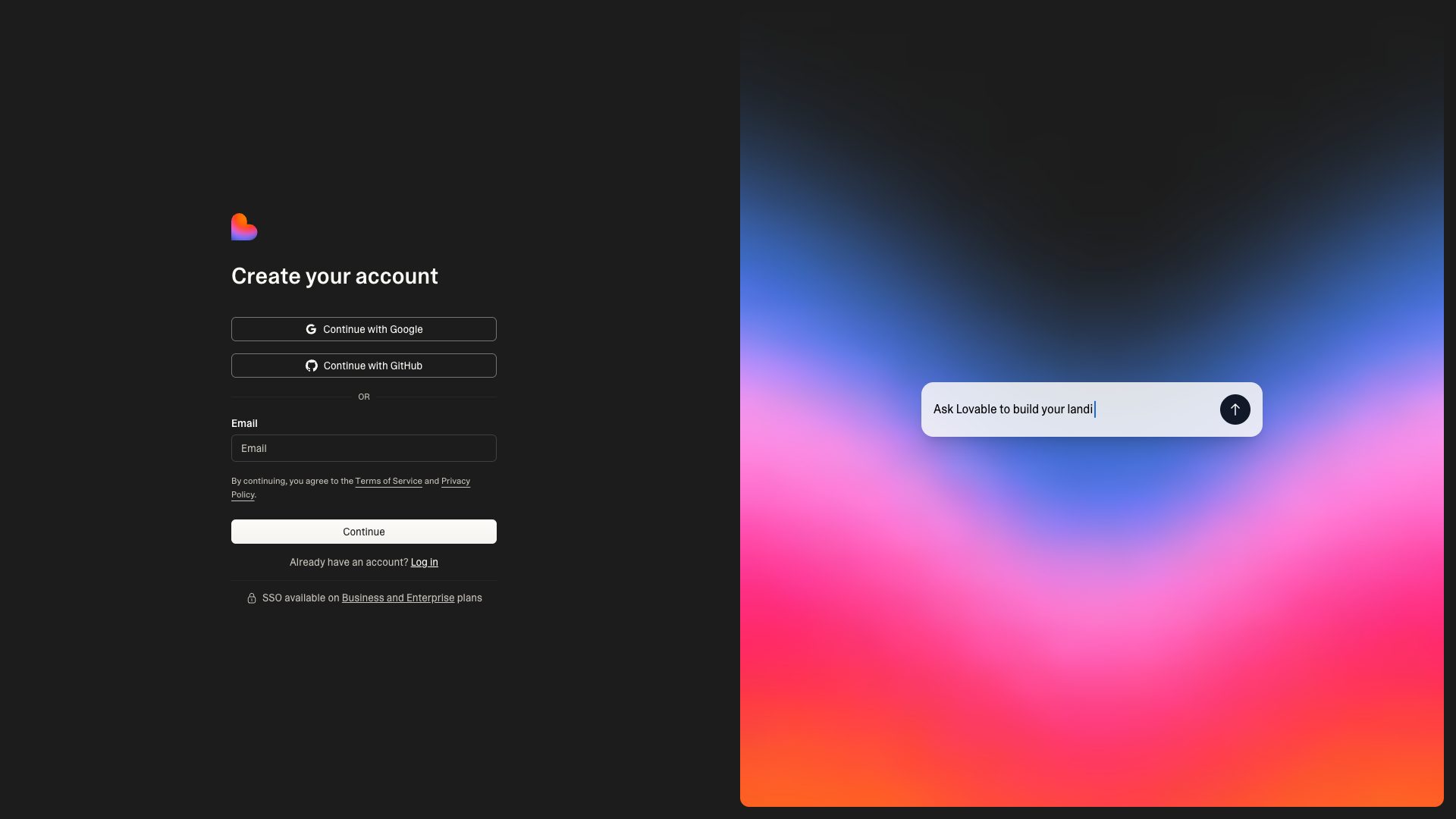
AI endpoint calls fired on page load without user action
CRIT P9
Prompt to Fix
In the signup/landing page, locate any code that initializes or calls AI/LLM endpoints on initial render. Move such calls to be triggered by user action (e.g., click to open AI widget). Implement lazy-loading, gating behind a consent toggle, and remove auto-triggered AI requests on page load.
Why it's a bug
The UI shows an AI prompt bubble and console indicates an AI endpoint is detected, implying LLM API calls occur during initial render. This can leak data, consume bandwidth, and violate user intent without consent.
Why it might not be a bug
If the design intentionally loads AI features immediately with explicit user consent, it could be acceptable; however, no visible user consent flow or lazy-loading is evident in the screenshot.
Suggested Fix
Delay all LLM/AI API calls until the user actively interacts with the AI feature (e.g., opening the chat). Implement lazy-loading and a clear consent/enable UX before initiating any AI requests. Remove any prefetch of AI prompts on page load.
Why Fix
Reduces unnecessary network usage, protects user privacy, and aligns with best practices for AI-enabled features.
Route To
Frontend Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
[DEBUG] JSHandle@error; ⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
N/A (no direct AI endpoint call shown in screenshot; issue inferred from console/logs)